In the ever-evolving landscape of digital security, it has become imperative for organizations to effectively safeguard their assets against an array of threats. Ensuring the confidentiality, integrity, and availability of sensitive information has transcended beyond a mere obligation, becoming an indispensable aspect of modern business operations. This comprehensive manual delves into the art of fortifying system security using the power of the widely acclaimed operating system and leveraging its innate capabilities.
Embarking on a journey through this guide will acquaint you with a host of intricate strategies aimed at establishing an impregnable defense mechanism. Employing this arsenal of tools enables you to bolster every facet of your organization's digital foothold to withstand the relentless onslaught of malicious actors. By following the guidelines set forth in this manual, you will gain invaluable insights into the intricate intricacies of employing holistic security policies that align with your organization's unique needs.
This manual aspires to empower you with a comprehensive understanding of the various facets involved in securing your systems to mitigate vulnerabilities and protect against attacks. From the art of designing robust access control mechanisms to implementing robust encryption algorithms, you will learn to harness the power of cutting-edge security features to safeguard your digital assets from unauthorized access, data breaches, and malicious intrusions.
Throughout this manual, we will explore various security measures, explore the nuances of privileged access management, and delve into the realm of audit trails and incident response. By familiarizing yourself with these key aspects, you will cultivate the expertise necessary to orchestrate a seamless security infrastructure, where every element synergizes to form an impenetrable fortress, impeding any malicious attempts to exploit your organization's vulnerabilities.
Exploring the Fundamentals of Security Protocols

In this section, we will delve into the underlying principles and concepts of security protocols that play a critical role in safeguarding sensitive information and systems. By gaining a deep understanding of these fundamental components, you will be equipped with the knowledge to effectively develop and implement robust security policies.
By comprehending the intricacies of security protocols, you can tailor your organization's policies to align with specific requirements, mitigating risks and ensuring the confidentiality, integrity, and availability of data. Through a comprehensive examination of the multifaceted aspects of these protocols, we will explore the different layers of security, authentication mechanisms, access controls, and encryption methods.
By grasping the importance of security protocols, you will be able to comprehend the significance of each layer within the stack and their contributions to establishing a secure computing environment. The examination of authentication mechanisms will unravel the means by which individuals or systems are verified, enabling you to tailor policies that enforce strict access controls while ensuring user convenience.
Furthermore, the exploration of encryption methods will equip you with the knowledge to select and implement appropriate algorithms and key management techniques to protect data at rest and in transit. Understanding the various encryption schemes will enable you to develop policies that strike the delicate balance between stringent security measures and operational requirements.
By the end of this section, you will have gained an in-depth understanding of security protocols, enabling you to make informed decisions when devising and managing security policies tailored to your organization's unique needs. With this knowledge, you will be well-prepared to navigate the complex landscape of securing systems and data in the modern digital age.
The Advantages of Windows in Security Policy Management
In this section, we will explore the numerous benefits that can be gained by utilizing the Windows operating system for managing security policies. Windows offers a range of features and functionalities that enhance the overall security of an organization, making it an ideal choice for efficiently managing security policies.
Enhanced Security Measures: Windows provides robust security mechanisms and advanced tools that allow administrators to implement and enforce effective security policies. These measures include user authentication, access controls, encryption, and auditing capabilities, ensuring that sensitive data and resources are safeguarded from unauthorized access.
Centralized Management: Windows offers centralized management capabilities, allowing administrators to easily define, monitor, and enforce security policies across multiple devices and user accounts. This streamlines the management process, reducing administrative overhead and ensuring consistent security configurations throughout the organization.
Scalability and Flexibility: Windows caters to organizations of all sizes, offering scalability and flexibility in security policy management. Whether you have a small business or a large enterprise, Windows provides the necessary tools and features to adapt security policies to meet specific requirements, ensuring optimal protection against evolving threats.
Integration with Active Directory: Windows seamlessly integrates with Active Directory, Microsoft's directory service, enhancing security policy management. Active Directory enables centralized user management, simplifies access control, and facilitates seamless authentication, further fortifying the security posture of the organization.
Robust Reporting and Compliance: Windows offers comprehensive reporting capabilities, enabling administrators to generate detailed reports on security policy compliance. These reports assist in identifying security vulnerabilities, monitoring policy enforcement, and ensuring compliance with industry regulations and standards.
Constant Updates and Support: Windows regularly releases updates, patches, and security fixes to address emerging threats and vulnerabilities. The ongoing support and maintenance ensure that security policies remain up-to-date and effective against the ever-changing landscape of cyber threats.
By leveraging the numerous advantages provided by Windows, organizations can establish a secure and well-managed environment, effectively protecting their assets and mitigating risks. The next section will delve deeper into the specific features and tools offered by Windows for managing security policies.
Creating a Security Policy in the Windows Environment
In this section, we will explore the process of developing a comprehensive security policy within the Windows operating system. By implementing a well-defined set of guidelines and practices, organizations can enhance the protection of their digital assets, mitigate potential risks, and ensure the confidentiality, integrity, and availability of their data.
When crafting a security policy, it is crucial to consider the unique needs and requirements of the organization. This involves identifying and assessing potential threats, vulnerabilities, and risks that could undermine the overall security posture. Once these factors have been evaluated, it becomes essential to establish a set of policies and procedures that address each aspect of security, including access control, network security, incident response, and data protection.
- Defining access control: This section outlines the rules and procedures governing user access to various resources within the Windows environment. It involves defining user privileges, role-based access control, password policies, and authentication mechanisms.
- Implementing network security measures: Here, we explore the methodologies and technologies employed to safeguard network infrastructure. It includes configuring firewalls, implementing intrusion detection/prevention systems, utilizing secure network protocols, and conducting regular vulnerability assessments.
- Establishing incident response protocols: This aspect focuses on defining the steps and actions to be taken in the event of a security incident. It involves procedures for reporting, containment, eradication, and recovery, as well as guidelines for conducting post-incident analysis and learning from security breaches.
- Safeguarding data: This section delves into strategies for protecting sensitive information stored within the Windows environment. It covers the implementation of encryption mechanisms, data backup procedures, access controls, and physical security measures.
- Ensuring compliance: Organizations must adhere to various industry standards and legal requirements. This part of the security policy focuses on ensuring compliance with regulations such as GDPR, HIPAA, or PCI-DSS, through the implementation of relevant controls and practices.
By following these guidelines and tailoring them to their specific needs, organizations can create a robust and effective security policy within the Windows environment. This policy will serve as a framework for maintaining a secure operating environment, protecting sensitive information, and preserving business continuity.
Step-by-Step Walkthrough: Crafting an Effective Security Policy
In this section, we will take you through a detailed step-by-step process to create a robust and practical security policy for your organization. This comprehensive guide will equip you with the essential knowledge and skills required to develop and implement an effective security framework.
Understanding the Importance
Before diving into the specifics, it's crucial to grasp the significance of crafting a well-defined security policy. A strong security policy serves as a guiding document that outlines the organization's commitment to safeguarding its assets, data, and infrastructure.
Mapping Organizational Objectives
The first step towards creating a security policy is to align it with the organizational objectives and values. By understanding the unique requirements and goals of your organization, you can tailor the policy to address the specific risks and challenges it faces.
Gathering Stakeholder Input
Developing a security policy necessitates collaboration and input from various stakeholders across the organization. Identifying key individuals and departments with valuable insights will ensure the policy caters to the diverse needs and perspectives within the organization.
Defining Scope and Framework
Clearly defining the scope and framework of the security policy establishes a solid foundation for its implementation. This involves defining the boundaries, responsibilities, and roles of different personnel in maintaining the security measures outlined in the policy.
Risk Assessment and Analysis
Conducting a comprehensive risk assessment is vital to identify potential threats and vulnerabilities that your organization might face. By carefully analyzing these risks, you can develop appropriate safeguards and controls to mitigate the impact of potential security breaches.
Establishing Policies and Procedures
Once the risks have been identified, the next step is to develop specific policies and procedures to address them effectively. These policies should cover various aspects such as data protection, access control, incident response, and user awareness training.
Regular Evaluation and Updates
Ensuring the continuous effectiveness of your security policy requires constant evaluation and updates. Periodically reviewing and assessing the policy will help identify areas for improvement and enable the organization to adapt to evolving security threats.
By following this step-by-step guide, you will be equipped to craft a comprehensive security policy that safeguards your organization's critical assets and fosters a culture of security awareness among its members.
Implementing and Enforcing Security Policies in the Windows Environment
Ensuring the proper implementation and enforcement of security policies is essential in maintaining the integrity and confidentiality of sensitive information within a Windows environment. This section provides an in-depth exploration of the strategies, techniques, and best practices required to effectively establish and uphold security policies in Windows.
- Understanding the Foundation of Security Policies
- Designing Robust Security Policies
- Implementing Access Control Mechanisms
- Monitoring and Auditing Security Policy Compliance
- Educating and Training Users
- Continuous Improvement and Adaptation
This section delves into the fundamental concepts and principles that underpin security policies, highlighting their critical role in safeguarding organizational assets. It explores the importance of defining and classifying assets, identifying potential threats and vulnerabilities, and establishing a risk management framework.
This part focuses on the development of comprehensive and tailored security policies based on the organization's specific requirements and industry standards. It covers the key components of policy development, including defining policy objectives, establishing clear guidelines and procedures, and incorporating industry best practices.
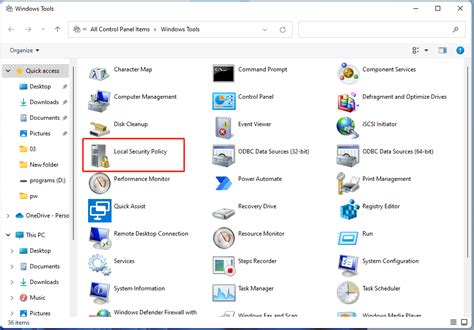
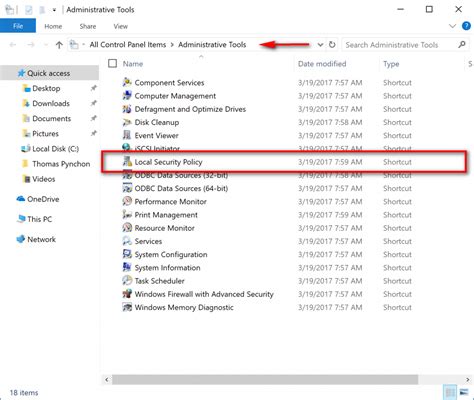
Access control is a crucial aspect of security policy implementation. This section explores various access control mechanisms available within the Windows environment, such as user account management, group policies, and permissions. It provides step-by-step guidance on configuring and managing access control to ensure authorized access and prevent unauthorized activities.
Regular monitoring and auditing are vital in ensuring the effectiveness of security policies. This part discusses the importance of implementing monitoring tools, creating audit trails, and conducting periodic assessments to identify policy violations and security breaches. It also highlights the significance of incident response and remediation measures.
Human factors play a significant role in maintaining security. This section emphasizes the relevance of user education and training in promoting adherence to security policies. It provides strategies for developing effective training programs, raising awareness about security risks, and fostering a culture of security-conscious users.
Security policies should continually evolve to address emerging threats and technological advancements. This part focuses on the importance of regularly reviewing, updating, and adapting security policies to ensure their relevance and effectiveness in a dynamic Windows environment. It also highlights the significance of conducting risk assessments and engaging in proactive measures to stay one step ahead of potential security pitfalls.
Tips for Effective Implementation of Security Policies
In this section, we will explore various strategies and recommendations for successfully implementing security policies in an efficient manner. Effective implementation of security policies serves as a cornerstone for ensuring a secure computing environment, safeguarding sensitive data, and mitigating potential risks. By following these tips, organizations can enhance their overall security posture and better protect their valuable assets.
Prioritize Policy Development
The first step towards effective policy implementation is to prioritize policy development. This involves conducting a thorough assessment of your organization's security needs, identifying potential vulnerabilities, and defining clear objectives for your security policies. By establishing a comprehensive policy framework tailored to your specific requirements, you can effectively address multiple security concerns and strengthen your overall security infrastructure.
Involve Stakeholders
Implementing security policies should involve collaboration and input from key stakeholders within your organization. By involving representatives from different departments and teams, you can ensure that the policies reflect the diverse perspectives and requirements of various stakeholders. This collaborative approach fosters a sense of ownership and accountability, leading to better adoption and compliance with the established security policies.
Regularly Assess and Update Policies
Security threats and technology landscapes are constantly evolving. Therefore, it is crucial to regularly assess and update your security policies to adapt to these changes effectively. Conduct periodic risk assessments, review emerging security best practices, and stay up-to-date with the latest industry trends. By continuously evaluating and refining your policies, you can maintain a dynamic security posture and effectively address emerging threats.
Provide Clear and Accessible Policy Documentation
Well-documented and easily accessible policy documentation is essential for successful policy implementation. Ensure that your policies are clear, concise, and written in a language that is easy to understand for all employees. Consider utilizing visual aids, flowcharts, and examples to enhance comprehension. Make the policy documentation readily available to all relevant stakeholders, either through a centralized document repository or an accessible intranet portal.
Establish Monitoring and Enforcement Mechanisms
Implementing security policies is not sufficient alone; it is equally important to establish robust monitoring and enforcement mechanisms. Regularly monitor adherence to policies, conduct internal audits, and implement appropriate controls to detect and prevent policy violations. Establish clear consequences for non-compliance and ensure that employees are aware of these consequences. These mechanisms play a vital role in maintaining policy integrity and enhancing overall security.
| Key Recommendations for Effective Implementation of Security Policies: |
|---|
| Prioritize policy development and tailor them to your organization's needs. |
| Involve stakeholders from different departments to gather diverse perspectives. |
| Regularly assess and update policies to address evolving security threats. |
| Provide clear and accessible policy documentation for all employees. |
| Establish monitoring and enforcement mechanisms to ensure policy compliance. |
Implementing Security Guidelines Throughout a Network

In this section, we will explore the effective methods to ensure the consistent enforcement of security policies across all connected devices within a network. By establishing and maintaining a robust security infrastructure, organizations can protect their valuable data and resources from potential threats and unauthorized access.
One crucial aspect of enforcing security policies is establishing a unified framework that encompasses all devices, systems, and applications present within the network. By creating a comprehensive set of guidelines and regulations, network administrators can establish a strong foundation for maintaining a secure environment.
Network segmentation plays a vital role in enforcing security policies across a network. By dividing the network into separate segments, each with its specific security measures and access controls, organizations can minimize potential vulnerabilities and limit the impact of security breaches. This approach helps to ensure that a single compromised device or system does not lead to unauthorized access or data loss throughout the entire network.
Continuous monitoring and auditing are essential to ensure the ongoing enforcement of security policies. By regularly assessing the network's security posture, administrators can identify potential weaknesses and promptly address them. Implementing robust monitoring tools and conducting regular audits allows organizations to detect and respond to security incidents effectively.
User awareness and training play a critical role in enforcing security policies across a network. Educating users about potential threats, best practices for password management, and safe browsing habits can significantly reduce the risk of security breaches caused by human error. Regular training sessions and awareness campaigns can help foster a security-conscious culture within an organization.
In conclusion, by implementing a comprehensive security framework, including effective network segmentation, continuous monitoring and auditing, and user awareness and training, organizations can establish a strong foundation for enforcing security policies across a network. This proactive approach allows for the protection of valuable data and resources, ensuring that potential vulnerabilities are minimized and promptly addressed.
Monitoring and Auditing Security Policies in Windows
In this section, we will delve into the crucial aspect of monitoring and auditing security policies in the Windows operating system. Understanding how to effectively monitor and audit security policies is essential for maintaining a secure environment and proactively addressing potential vulnerabilities.
1. Importance of Monitoring Security Policies: Monitoring security policies allows administrators to track the implementation and enforcement of various security measures in the Windows system. It provides insight into the effectiveness of the policies, identifies potential weaknesses, and helps ensure compliance with organizational security standards.
- ✓ Regular monitoring enables proactive identification and mitigation of security breaches
- ✓ It allows administrators to detect policy violations and unauthorized access attempts
- ✓ Monitoring aids in identifying trends and patterns to improve overall security posture
2. Key Elements of Monitoring: Monitoring security policies involves observing and analyzing relevant security logs, events, and activities within the Windows environment. The following key elements play a significant role in effective monitoring:
- ✔ Windows Event Logs: Understanding the different types of event logs and their contents
- ✔ Log File Management: Implementing proper log file management practices
- ✔ Real-time Monitoring: Utilizing real-time monitoring tools to capture security-related events
- ✔ Alerting Mechanisms: Configuring alerts and notifications for critical security events
3. Auditing Security Policies: Auditing serves as a complementary approach to monitoring. It involves the examination and analysis of security policies, configurations, and activities to ensure compliance and identify potential risks. This section will cover the following aspects of auditing:
- ✓ Auditing principles and best practices
- ✓ Determining the scope and frequency of audits
- ✓ Reviewing and analyzing audit logs and reports
- ✓ Taking corrective actions based on audit findings
By comprehensively monitoring and auditing security policies in Windows, organizations can proactively address security issues, identify and mitigate vulnerabilities, and maintain a robust security posture.
Exploring Tools and Strategies for Monitoring Security Policies

In this section, we delve into the various tools and techniques available for effectively monitoring and enforcing security policies in a Windows environment. By utilizing a range of cutting-edge methodologies and technologies, organizations can ensure the protection of their systems and data against potential threats and vulnerabilities.
One crucial aspect of monitoring security policies is the ability to track and analyze events and activities that occur within an IT infrastructure. This can be achieved through the deployment of advanced auditing and logging mechanisms that provide detailed insights into user actions, system changes, and network events. These tools offer real-time visibility and generate comprehensive reports, enabling administrators to identify any potential security breaches or policy violations.
Another essential component of monitoring security policies involves the implementation of robust intrusion detection systems (IDS) and intrusion prevention systems (IPS). These tools actively monitor network traffic and analyze it for patterns that indicate malicious activities or unauthorized access attempts. By promptly detecting and mitigating potential threats, organizations can proactively defend their systems and prevent data breaches or system compromise.
Additionally, organizations can leverage powerful security information and event management (SIEM) platforms that provide a centralized approach to security policy monitoring. These platforms collect data from multiple sources, including network devices, servers, and applications, and perform advanced analysis to identify security incidents and policy breaches. With their comprehensive reporting capabilities and real-time alerting mechanisms, SIEM solutions enable administrators to effectively manage and respond to security events.
Furthermore, organizations should consider employing behavior analytics tools that utilize machine learning and artificial intelligence algorithms to detect anomalies and deviations from expected user behavior. By establishing behavior baselines and continuously monitoring user actions, these tools can identify suspicious activities that may indicate insider threats or compromised user accounts.
Table 1 illustrates a comparison of some commonly used monitoring tools and techniques, highlighting their features and functionalities. By exploring and implementing a combination of these tools, organizations can establish an efficient security policy monitoring framework, bolstering their overall cybersecurity posture.
| Tool/Technique | Features | Functionality |
|---|---|---|
| Auditing and logging mechanisms | Real-time visibility, comprehensive reporting | Track user actions, system changes, and network events |
| Intrusion detection systems (IDS) | Network traffic monitoring, threat detection | Detect and mitigate potential threats |
| Intrusion prevention systems (IPS) | Real-time threat prevention, anomaly detection | Prevent data breaches and unauthorized access attempts |
| Security information and event management (SIEM) | Centralized data collection, advanced analysis | Identify security incidents and policy breaches |
| Behavior analytics tools | Machine learning, anomaly detection | Detect suspicious activities and insider threats |
The Significance of Regular Auditing for Ensuring Security Compliance
Regular auditing plays a critical role in maintaining and enforcing security measures to ensure compliance with the established standards and regulations. By conducting regular audits, organizations can proactively assess their security systems, identify potential vulnerabilities, and take appropriate measures to mitigate risks and protect their valuable assets.
An audit involves a systematic and comprehensive evaluation of security controls, policies, and procedures implemented within an organization. It helps to validate the effectiveness of the security measures in place and identify any gaps or deficiencies that may exist. Regular audits enable organizations to stay up-to-date with the evolving security landscape and ensure that their security practices align with the latest industry standards and best practices.
Moreover, regular auditing provides valuable insights into the overall security posture of an organization. By analyzing audit findings and reports, management can make informed decisions regarding security investments and prioritize areas that require improvement. Audits also help demonstrate compliance with legal and regulatory requirements, thereby reducing the risk of fines, penalties, and reputational damage.
In addition to the benefits of compliance and risk mitigation, regular auditing fosters a culture of continuous improvement within an organization. It encourages a proactive approach towards security and helps in identifying and addressing security issues before they escalate into major incidents. Audits not only evaluate security controls but also assess the effectiveness of security policies and training programs, ensuring that employees are aware of their responsibilities and adhere to the established security protocols.
In conclusion, the importance of regular auditing cannot be overstated when it comes to maintaining security compliance. By regularly evaluating and assessing security controls, organizations can enhance their security posture, minimize risks, and demonstrate their commitment to protecting sensitive information and assets.
[MOVIES] [/MOVIES] [/MOVIES_ENABLED]FAQ
What is the purpose of the article "Using Windows to Manage Security Policies: A Comprehensive Guide"?
The purpose of the article is to provide a comprehensive guide on using Windows to manage security policies.
What are security policies in the context of Windows?
In the context of Windows, security policies are a set of rules and settings that govern the security of a computer system. They define how users and groups can interact with the system and what actions they are allowed or denied.
Why is it important to properly manage security policies in Windows?
Properly managing security policies in Windows is important to ensure the confidentiality, integrity, and availability of the computer system. It helps protect against unauthorized access, data breaches, malware infections, and other security threats.
What are some common security policy management tasks in Windows?
Some common security policy management tasks in Windows include creating and modifying security policies, assigning user rights and permissions, defining password policies, auditing system events, and enforcing security settings across multiple systems.
What are the recommended best practices for managing security policies in Windows?
The recommended best practices for managing security policies in Windows include regularly reviewing and updating security policies, using strong and unique passwords, limiting user privileges, enabling audit logging, keeping the system up to date with the latest security patches, and regularly monitoring system logs for any suspicious activities.
What is the importance of managing security policies in Windows?
Managing security policies in Windows is crucial for maintaining the integrity, confidentiality, and availability of sensitive data and resources. It allows organizations to control access to systems, define user privileges, enforce password policies, and mitigate security vulnerabilities. Implementing effective security policies helps protect against unauthorized access, data breaches, malware attacks, and other security threats.
What are some common security policies that can be managed in Windows?
Windows provides the flexibility to manage various security policies. Some common policies include password complexity requirements, account lockout settings, user privileges, remote access policies, firewall configurations, antivirus and antimalware settings, audit policies, encryption policies, and application control. These policies can be customized and enforced according to an organization's specific security needs.